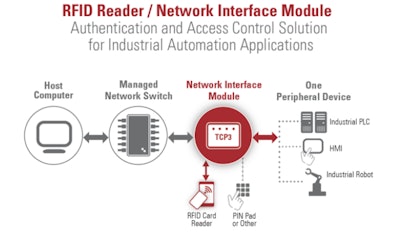
A typical manufacturing plant has a diverse assortment of machinery, robots, and flexible manufacturing systems that fabricate and assemble various products. These machines are often driven by programmable automation controllers (PLCs, Industrial PCs, robots) and use a human-machine interface (HMI) for configuration, notifications and routine control.
The automation controllers have software programs that perform specific tasks in a logical order to drive the machine or process. With automated systems growing in number and increasingly interconnected, programmable automation controllers and HMI software access control are crucial.
Automation controllers are usually connected through plant-wide Ethernet networks to IT servers that include databases for collecting and storing information to manage things like employee identity and authorization to run and support plant manufacturing processes. Identified plant personnel authorized to change or update automation controller and HMI software is stored on IT servers.
Authorization data determine if the employee has the proper skill set, is currently trained and certified to access the manufacturing system hardware and software. Equally important is if an employee is authorized to enter a hazardous area to perform maintenance or other activities.
Plant IT servers typically store copies of the machine automation controller (PLCs and PCs, and robot) and HMI software for backup, change control, and disaster recovery purposes. To prevent unauthorized software updates, a user authentication system should be installed on or near the operator station, requiring the physical presence of the person authorized to update or make changes to the software. This added authentication and authorization requirement further protects the manufacturing system, engineers, machine operators and maintenance personnel.
Access to Automation Controller Software & Change Control a Problem for the Plant Control Engineer
Working with the IT department, plant control engineers are usually responsible for authorization to access plant automation controller and HMI software. Authorized personnel typically include plant engineers, maintenance electricians and IT personnel who can access software running specific processes. The level of access varies according to the individual’s function in the plant.
Engineers usually have full access to upload, download and change controller and HMI software. IT personnel usually have only upload or download authorization for backup and disaster recovery purposes. Plant maintenance electricians typically have limited access to change software and only for process troubleshooting. The specific authorization may vary from plant-to-plant, but identification of who accessed the software, who made changes and at what time is logged in a database to track changes for review when necessary.
There are many reasons control engineers design systems that log and track software changes to automation controllers and HMIs. One primary reason is that the impact of unauthorized changes is often severe and may include one or more of the following effects:
- Loss of production
- Undesirable changes to product quality
- Lengthy process startup time or downtime
- Engineers, operators, and maintenance personnel on different shifts unaware of changes, who made them, or when
- Software changes not backed up to IT servers
- Creation of unsafe operating conditions
RFID Solution for Implementing Access Control to Industrial Automation Controller & HMI Software
Authentication and authorization systems for access control of software in industrial automation applications in factories today require that they be easy to use, flexible, durable, secure, and stand up well to environmental elements. RFID card systems address these application requirements better than magnetic stripe cards, smart (chip) cards and PIN pads. RFID cards are the most widely used form of authentication and access control today.
The diagram below shows a solution for authentication and access control of industrial automation software using an RFID reader combined with a network interface module.
Benefits of RFID Card Systems
One of the essential benefits of RFID authentication and access control is that it is easy and convenient for users. RFID cards are touchless, and the user only has to wave the card within a few inches of the reader to be read.
RFID readers are used throughout the organizational ecosystem for multipurpose authentication using existing employee building-entry ID cards. Functionality such as time-based access control, access to manufacturing processes, access to automation controller and HMI software and hazardous areas can be added. Additionally, RFID readers can often read and write to more than one type of card. Should plant requirements change, cards can be updated without issuing a new card.
When enabled with network access, readers can communicate using various communication protocols, including gigabit Ethernet, with information technology systems and industrial automation applications like industrial programmable controllers, HMIs, and robots.
Since they are touchless, both cards and the readers experience less wear and tear than in systems requiring the card to contact the reader, such as in magnetic stripe cards and smart (chip) card systems. Over time, this can minimize the replacement cost of both cards and readers.
RFID card systems are more secure than other card-based identification technologies. Data transfer between cards and readers and message traffic between card readers and plant networks can be encrypted.
RFID readers and cards can also execute a kill command if the card is lost or stolen. Since the kill command deactivates the card, it prevents unauthorized access to sensitive data, hardware and software that controls industrial manufacturing processes and hazardous areas in the plant.
Importantly, given industrial settings, RFID cards and readers are more durable in harsh plant floor environments against dust, heat, dirt and general wear and tear than other authentication and access control technologies.
RFID is a secure, flexible, reliable, and easy to use solution for authentication and access control of hardware and software in industrial automation processes and hold up well in harsh plant floor environments. There are multiple RFID reader technologies on the market, but they are not all created equal. Choosing a comprehensive authentication and access control platform that offers a wide range of options can help your organization implement a solution to control access to industrial automation software that will continue to meet your needs now and as they change over time.
Chris Randle is vice president of industry solutions for ELATEC Inc, headquartered in Palm City, Florida. His team provides consultation and support to OEMs, software developers, and integrators. Chris has more than 20 years of experience with customer product management and engineering teams to design and integrate embedded electronic technologies.