Since industrial networks are primarily built and expanded to address growing business demands, it may be easy for administrators to overlook common system vulnerabilities. For example, when adding a device to a newly built or expanded network, do you know which industrial Ethernet switches have unlocked ports? Or, do you simply connect new devices without a second thought?
It must not be forgotten that ignoring common system vulnerabilities in today’s world could put your entire network at risk. The following scenarios summarize some common system vulnerabilities in industrial networks that may be exploited during the three main stages of a cyberattack: exploration, utilization, and attack.
Stage 1: Exploration and Infiltration
Recall the last time you logged onto your network. How complex was your password? Although weak passwords may be easier for busy administrators to remember, they are also easier for malicious actors to crack through a brute force attack. Making it easy for an attacker to guess your network login credentials is like putting the keys to your house in a location that is easy for a robber to find.
Attackers commonly exploit open ports on networks. For instance, Ethernet switches act as gates through which information is sent and received on networks. If you leave the door open, intruders can walk right in. By scanning your network, hackers can identify open ports and infiltrate your network just like a burglar entering through an unlocked gate.
How to Mitigate: One of the simplest ways to enhance your network security is to ensure that users create a sufficiently complex password to reduce the likelihood of an attacker guessing your credentials by brute force. For additional security, you should also consider a login failure lockout mechanism that limits the number of unsuccessful login attempts, which may indicate a brute-force attack. To protect your network from port scanning, you can create a whitelist of ports that are accessible through your firewall and also disable WAN pinging.
Stage 2: Utilization and Network Control
During the second stage of a cyberattack, the malicious actor has already infiltrated the network and is using resources on the network for their own purposes. Even though they are not actively wreaking havoc on the network, they are secretly gathering information and laying the groundwork for a more harmful attack.
For example, a hacker may be using various scanning tools to learn about your network topology so that they can find their next target and access or control more devices. The attacker can even use command injection to bypass authentication requirements or grant themselves higher levels of user privileges to execute prohibited commands and commandeer network devices for nefarious purposes.
How to Mitigate: To limit the attacker’s ability to move throughout your network and commandeer your devices, we recommend network segmentation and traffic control. For example, you should partition your network into smaller segments and control the communications that pass through these segments. In addition, deploying whitelist control to prevent command injection can also limit the severity of the security breach.
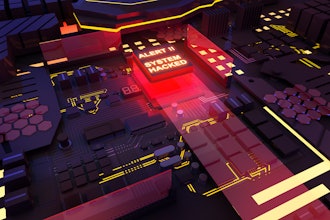
Stage 3: Services and Data Disruption
Stealing or destroying critical business data from networks will be costly and harmful to any organization. However, these malicious actions are far from the worst case scenario of a successful cyberattack. During the last stage of a cyberattack, the hacker is no longer studying networks but actively causing damage.
During stage 3 of a cyberattack, the hacker could make a machine or network resources unavailable to authorized users by temporarily or indefinitely disrupting services on a host. This is typically called a Denial of Service (DoS) attack, which involves flooding a targeted machine in an attempt to overload it with pings. Furthermore, a hacker could unleash malware, including ransomware to deny you access to your network resources until a ransom is paid.
How to Mitigate: Although damage has already been done by the time the cyberattack reaches stage three, you can still mitigate the overall harm to your network by ensuring sufficient DoS or DDoS (distributed DoS attacks that involve multiple systems) protection and deploying industrial IPS for ransomware and other malware. You should also maintain reliable system backups and blacklist unauthorized protocols to minimize data loss.
With cyberattacks targeting more and more industrial networks, it is crucial to identify and mitigate system vulnerabilities before these weaknesses are exploited by those who intend to do harm.
There are two directions you can take to enhance network security. One is to ensure that your industrial networks have a foundation–secure network infrastructure, which allows authorized traffic to flow to the correct places. Alternatively, you can identify critical assets and give them layered protection, such as industrial IPS or whitelisting control.
To learn more about Moxa’s industrial cybersecurity solution, please visit www.moxa.com/security.